As phishing attacks rise, knowledge of common phishing trends is the greatest weapon to combat them While phishing attacks have decreased from 2022 to 2023, consequences from these attacks are soaring, with a 144% increase in financial penalties and a 50% increase in reputational damages year over year due to phishing attacks, according to Proofpoint’s 2024 State of the Phish report. Scammers' … [Read more...] about Phishing Trends and Techniques You Need to Know
Identifying and Analyzing Threats in OPSEC
How to complete the second step of OPSEC effectively Operations Security, or OPSEC, is a five-step process that aims to prevent adversaries from accessing sensitive or classified information. These five steps are identifying the sensitive information that needs to be protected, identifying threats to that information, analyzing your company or contract’s vulnerabilities, assessing the risk the … [Read more...] about Identifying and Analyzing Threats in OPSEC
Addressing Physical Vulnerabilities for Your Small Business
Ensure your business is safe from intruders no matter your budget When starting a brick-and-mortar small business, the last thing you want to worry about it is a break-in. Addressing your business’s physical vulnerabilities from the beginning can help save you heartache down the road. While there’s a wide range of security measures you can take, you can find ways to have strong security on a … [Read more...] about Addressing Physical Vulnerabilities for Your Small Business
Your Guide to Derivative Classification
Understand derivative classification and how to avoid common mistakes Derivative classification is the process of creating new classified information from existing classified information, and understanding how to create it can be an important skill for those holding a Personnel Clearance (PCL). Derivative classified information can’t be created by just anyone, but if it’s part of your cleared … [Read more...] about Your Guide to Derivative Classification
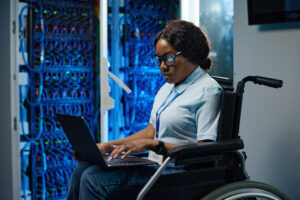
Disability Accessibility Concerns in SCIF Construction
What Issues do SCIFs Face in Relation to ADA Compliance? The Government Accountability Office (GAO) recently released a report that found that the federal agencies using SCIFs and SAPFs have failed to consistently address accessibility for disabled people in their facilities. SCIFs fall under requirements from the Office of the Director of National Intelligence (ODNI), and GAO found that “ODNI … [Read more...] about Disability Accessibility Concerns in SCIF Construction
Best Practices to Maintain and Enact an Emergency Action Plan
Keep your company and facility ready to respond to any possible emergencies Whether it’s the earthquake drill often practiced in elementary schools or the blaring fire alarms alerting an office to head outside, Emergency Action Plans (EAPs) play a significant role in all areas of life and work. And while they might feel tedious or monotonous at times, that is for good reason. Some of the … [Read more...] about Best Practices to Maintain and Enact an Emergency Action Plan
Protecting Classified Information During Emergencies at Your Cleared Facility
What should you do with classified information during an emergency? For any company that holds a Facility Clearance (FCL) and is thus approved to access classified information, having a Facility Security Officer (FSO) who knows how to protect that material during emergencies is essential. Companies that hold or store classified information are known as possessing facilities. All are required to … [Read more...] about Protecting Classified Information During Emergencies at Your Cleared Facility
How to Protect Yourself From Identity Theft
Tips on how to protect your PII to keep it out of scammers’ hands Identity theft remains the most common type of fraud in the U.S., and having your identity stolen can come with a hefty price tag or cost you your credit score. There were more than 1.1 million reports of identity theft made to the Federal Trade Commission in 2022. Typically, criminals will attempt to steal your information … [Read more...] about How to Protect Yourself From Identity Theft
How Will AI Impact the Future of Security?
Is AI something to fear, or a tool you can learn to use? Artificial Intelligence, or AI, is developing at a breakneck speed. While there are many innocuous uses, like using it to generate the most bizarre art prompts you can think of, it could pose a risk to your company security. At the same time, it could be harnessed to help strengthen your security. AI is evolving at such a rapid pace … [Read more...] about How Will AI Impact the Future of Security?